Blog
Healthcare Data Center Compliance: The Enterprise Guide to Infrastructure Security
In 2023, the Office for Civil Rights reported that healthcare data breaches affected over 133 million individuals, a figure that highlights the high stakes of modern infrastructure security. You likely understand that maintaining healthcare data center compliance isn’t just about checking a box; it’s about avoiding the multi-million dollar penalties that stem from even the smallest oversight. It’s frustrating when you’re unsure where your colocation provider’s responsibility ends and yours begins, especially when you can’t physically audit a remote facility every week.
We’ve built this guide to help you master the complexities of HIPAA and HITECH requirements. You’ll learn how to ensure your data center infrastructure meets the highest standards of protection for sensitive patient information. We’ll provide a clear framework for auditing colocation providers, explain the nuances of Business Associate Agreements (BAA), and show you how to maintain a stable, super-fast environment for mission-critical PHI. By the end of this article, you’ll have a concrete strategy to secure your data and eliminate the fear of third-party negligence.
Key Takeaways
- Understand how HIPAA and HITECH standards dictate the physical and technical security of your infrastructure to protect sensitive patient data.
- Identify the three essential pillars of security—physical, technical, and administrative—required to safeguard every layer of your data environment.
- Learn how to structure a Business Associate Agreement (BAA) to clearly define legal responsibilities between your organization and your infrastructure provider.
- Master the 2026 audit process by identifying critical security indicators in SOC 2 Type II reports and evaluating physical access protocols.
- Discover why enterprise-grade colocation offers a more secure and scalable foundation for healthcare data center compliance than traditional on-premise solutions.
Understanding the Regulatory Framework for Healthcare Data Center Compliance
Healthcare data center compliance centers on the protection of sensitive patient data through rigorous physical and technical safeguards. It is not just a suggestion; it’s a legal mandate for any facility handling Protected Health Information (PHI). Data centers must secure PHI at rest on storage arrays and in transit through networking equipment. Modern infrastructure requires a combination of biometric access controls, encrypted backups, and redundant power systems to meet these high standards. When an enterprise chooses a data center, they are selecting a partner responsible for the foundational security of their medical records.
The framework evolved significantly with the HITECH Act of 2009. By 2026, the Department of Health and Human Services (HHS) expects even stricter enforcement of technical safeguards and audit trails. This evolution shifted the primary responsibility from the healthcare provider alone to the data center operator. Every byte of data must be accounted for, and every access point must be logged to prevent unauthorized exposure.
HIPAA vs. HITECH: What Every IT Director Needs to Know
HIPAA established the baseline for privacy and security in 1996. HITECH expanded these rules in 2009 to address the massive digital shift in medicine. IT directors must understand that HITECH made data center operators directly liable for breaches. Under the mandatory breach notification rule, facilities have exactly 60 days to report a data compromise to the HHS. HIPAA and HITECH act as a unified regulatory shield that governs every byte of patient data processed within a facility as of 2026.
The Concept of the Business Associate in Colocation
Every modern colocation provider is a Business Associate (BA) if they host PHI. Even “zero-access” facilities, where the provider doesn’t have keys to the client’s cabinet colocation space, fall under this category. The legal status has shifted from “conduit” to “maintenance” status for most providers. This means providers are responsible for the physical environment and the integrity of the hardware supporting the data. Subcontractors who assist with server maintenance or physical security also need to sign Business Associate Agreements (BAAs) to maintain the compliance chain.
Compliance in 2026 involves more than just a locked door. It requires a proactive stance on servers and monitoring systems to detect anomalies before they become breaches. Data centers must demonstrate they have the technical maturity to handle the specific needs of the healthcare sector, including high-availability power and cooling that prevents data corruption during outages.
The Three Pillars of Data Center Compliance: Physical, Technical, and Administrative
Achieving robust healthcare data center compliance requires a multi-layered strategy that addresses every potential point of failure. The HIPAA Security Rule establishes a framework built on three specific pillars: physical, technical, and administrative safeguards. These pillars don’t just protect against data breaches; they ensure the “Availability” requirement of healthcare data is met at all times. If one pillar fails, the entire compliance posture collapses, leaving sensitive patient information vulnerable and the enterprise liable for significant penalties.
Hardened Physical Security Measures
Physical security is the first line of defense for healthcare data center compliance. Facilities must implement biometric access controls, such as fingerprint or iris scanners, to ensure that only authorized personnel enter sensitive areas. This is paired with 24/7/365 high-definition video surveillance that monitors every entry point and server aisle. To prevent unauthorized entry through tailgating, modern facilities utilize man-traps and strict visitor logging protocols that require government-issued identification for every guest.
For enterprises handling large volumes of PHI, standard shared environments often fall short of internal audit requirements. Utilizing private colocation suites provides a necessary layer of isolation. These suites allow healthcare providers to wall off their hardware from other tenants, ensuring that physical access is restricted solely to their specific team and vetted data center technicians. This level of separation is a critical component for passing rigorous SOC 2 Type II and HIPAA audits.
Technical Integrity and Connectivity
Technical safeguards focus on the data itself and the networks it travels across. Encryption is mandatory for data in transit and at rest. To prevent data interception at the physical layer, enterprises rely on secure cross-connect services. These direct, point-to-point cable connections between providers within the data center bypass the public internet, significantly reducing the attack surface for hackers.
Redundancy is another technical mandate. N+1 power redundancy ensures that if a primary power source or generator fails, a backup is immediately available to take the load. Redundant power systems are mandated by compliance standards because a loss of power directly results in a loss of data availability, violating the federal requirement to ensure PHI is accessible when needed. Maintaining 100% uptime isn’t just a performance goal; it’s a legal necessity for healthcare providers who depend on real-time data for patient care.
Administrative Safeguards and Risk Management
The final pillar involves the policies and people governing the technology. Administrative safeguards include mandatory workforce training and the implementation of clear incident response plans. Enterprises must conduct regular risk assessments to identify vulnerabilities before they are exploited. These assessments must be documented and updated at least once a year or whenever significant changes are made to the infrastructure. By aligning these three pillars, organizations create a stable environment where data remains confidential, intact, and ready for use. If you are looking to strengthen your infrastructure, exploring secure cabinet options can provide the dedicated environment your compliance team requires.
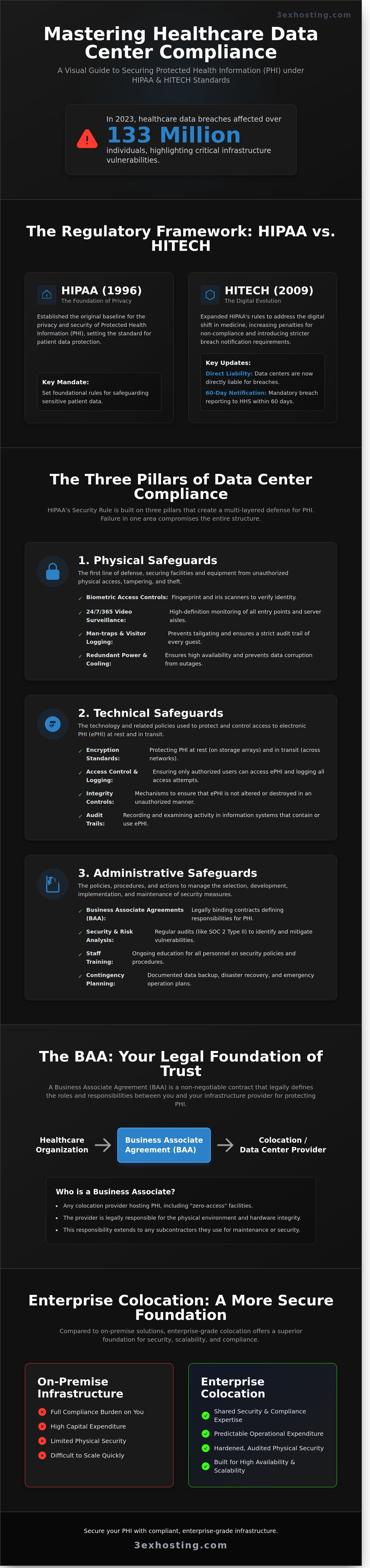
The Business Associate Agreement (BAA): The Legal Foundation of Trust
A Business Associate Agreement (BAA) serves as the primary legal mechanism for establishing healthcare data center compliance. It’s not a mere formality. According to the Department of Health and Human Services (HHS), any third party handling Protected Health Information (PHI) must sign a BAA. This document shifts liability and ensures the data center provider understands its role under the HIPAA Security Rule. Without a specific BAA, a healthcare provider remains fully liable for any breach occurring within the data center’s walls.
To satisfy Office for Civil Rights (OCR) requirements, the agreement must define the scope of responsibility with surgical precision. A common point of failure is the “gray area” between the operating system and the physical hardware. In a typical colocation environment, the provider manages the physical cage, power, and cooling, while the healthcare enterprise manages the OS and applications. Your BAA should explicitly state that the provider is responsible for physical access controls, while you retain control over logical access. Relying on “template” BAAs is a high-risk strategy. These generic forms often ignore physical infrastructure nuances, such as biometric log retention or the specific protocols for escorted versus unescorted access.
Key Clauses for Infrastructure BAAs
Practical clauses make the difference during a federal audit. You must include strict reporting requirements for security incidents. While HIPAA allows up to 60 days to report a breach, enterprise-grade agreements usually mandate notification within 24 to 48 hours. Right-to-audit clauses are equally vital. These ensure you can verify the facility’s claims by reviewing their SOC 2 Type II reports or physical access logs. Finally, the BAA must dictate data destruction protocols. Any decommissioned hardware must be handled according to NIST 800-88 standards to prevent data remnants from leaking during the disposal process.
Subcontractor Management
Compliance doesn’t stop at the primary provider; it flows down to every subcontractor. This includes specialized maintenance staff and third-party technicians. It’s critical that remote hands support teams receive documented HIPAA training. They must understand the “minimum necessary” access rule, which dictates that personnel only access the physical areas or systems required to perform their specific task. In 2022, approximately 13% of healthcare data breaches involved third-party vendors. This statistic highlights why subcontractor oversight is a non-negotiable part of your healthcare data center compliance strategy. Ensure your provider maintains a list of authorized subcontractors and requires them to sign downstream BAAs that are just as rigorous as your own.
Auditing Your Infrastructure Provider: A Compliance Checklist for 2026
Compliance doesn’t end when you sign a Service Level Agreement (SLA). It’s a continuous process of verification. To maintain healthcare data center compliance, you must treat your infrastructure provider as an extension of your own team. In 2026, surface-level checks aren’t enough to satisfy auditors or protect patient records from sophisticated threats.
Start by analyzing SOC 2 Type II reports. Don’t just look at the cover page. Dive into the “Security” and “Availability” categories. A Type II report is superior to Type I because it proves the provider maintained controls over a 6 to 12-month period, rather than a single day. Verify that the auditor found zero “exceptions” in the controls governing your data. If exceptions exist, ask for the remediation plan immediately.
- Physical Access: Review CCTV logs. High-security facilities should retain footage for at least 90 days. Ensure biometric entry points require dual-factor authentication.
- Disaster Recovery: Verify the Disaster Recovery (DR) and Business Continuity (BC) plans. A provider should demonstrate a Recovery Time Objective (RTO) of less than 4 hours for critical infrastructure.
- Support Testing: Conduct a “silent” test. Trigger a simulated incident and measure the response time. For healthcare environments, a 15-minute response window for P1 issues is the professional standard.
- Environmental Resilience: Confirm the stability of the full cabinet colocation environment. This includes checking N+1 or 2N redundancy for power and cooling systems.
The Annual Compliance Audit
Perform a physical walkthrough of the facility every 12 months. Test the biometric controls yourself. Review power and cooling logs to identify any fluctuations that could signal future instability. Ensure the provider performs internal vulnerability scans on their management networks every 90 days. This prevents lateral movement if a breach occurs at the administrative level. Stability is the foundation of security.
Compliance Beyond HIPAA: SOC 2 and ISO 27001
It’s a common misconception, but a “HIPAA-certified” data center doesn’t legally exist. The OCR doesn’t provide certifications. Instead, healthcare data center compliance relies on SOC 2 Type II and ISO 27001:2022. ISO 27001 is particularly vital if you handle data for international patients, as it aligns with global standards like GDPR. These audits serve as a legal proxy, proving the provider meets the rigorous administrative and technical safeguards required by the HIPAA Security Rule.
Ready to secure your medical data in a facility built for 100% uptime? Explore our compliant data center solutions today.
Enterprise Colocation: The Secure Foundation for Mission-Critical Healthcare Data
On-premise server rooms often fall short of the rigorous demands of healthcare data center compliance. Most private medical facilities lack the multi-million dollar capital investment required to build a Tier III equivalent environment. Enterprise-grade colocation fills this gap. It provides a hardened physical shell, redundant power, and advanced cooling that most internal IT closets can’t match. By moving hardware to a specialized facility, organizations shift the burden of physical security and environmental monitoring to experts who specialize in 100% uptime.
For health-tech firms experiencing rapid growth, cage solutions offer a scalable path that evolves with the business. You don’t need to rebuild your entire infrastructure when your data footprint expands by 35% or 50% year-over-year. Instead, you secure a dedicated perimeter that ensures your hardware remains physically isolated from other tenants. This physical separation is a critical component of a comprehensive compliance strategy, providing an extra layer of protection against unauthorized access.
3EX Hosting delivers the high-density infrastructure essential for modern medical imaging and Electronic Health Record (EHR) systems. High-resolution PACS (Picture Archiving and Communication Systems) files require massive throughput and reliable storage. Our facility handles power densities that would overwhelm standard office cooling systems. We provide a carrier-neutral environment with redundant fiber paths from multiple providers. This ensures your connection stays live even if a primary line is cut, keeping patient data accessible to clinicians 24/7.
Mission-Critical Uptime and Security
Data loss in healthcare isn’t just a financial risk; it’s a patient safety issue. We leverage high-performance infrastructure to maintain constant availability for your applications. Our 24/7/365 onsite technical experts provide a rapid response to any hardware concerns. This means your internal team doesn’t have to manage facility emergencies in the middle of the night. Your hardware sits in a facility designed for enterprise resilience, featuring multi-factor biometric access controls and constant video surveillance to satisfy healthcare data center compliance audits.
Next Steps: Securing Your Healthcare Infrastructure
Moving from an on-premise setup to a compliant colocation environment requires a structured plan. Start by reviewing your current hardware lifecycle and identifying which systems require immediate migration. You must request a Business Associate Agreement (BAA) and a recent facility audit report from your provider to verify they meet HIPAA standards. These documents are the backbone of your compliance folder.
Don’t leave your infrastructure to chance. Contact 3EX Hosting for a consultation. We help you build a compliant infrastructure solution that protects your patients and your reputation. Our team understands the technical nuances of medical data hosting and provides the stability your organization needs to grow.
Future-Proofing Your Healthcare Infrastructure
Maintaining healthcare data center compliance isn’t a one-time task; it’s a continuous commitment to patient privacy and system uptime. The shift toward 2026 auditing standards requires a rigorous focus on the three pillars of security. Physical safeguards, technical controls, and administrative policies form a shield around sensitive PHI. A solid Business Associate Agreement ensures your legal protection while enterprise-grade colocation provides the technical foundation you need. Relying on outdated infrastructure leads to vulnerabilities that modern healthcare demands can’t tolerate.
3EX Hosting delivers the stability your mission-critical applications require. Our facilities feature N+1 power redundancy to prevent downtime. We also provide 24/7 Remote Hands Support for immediate technical assistance. Our enterprise-grade high-density infrastructure handles the most demanding medical workloads without compromise. You don’t have to navigate these complex regulatory requirements alone when you have a partner focused on technical excellence and reliability.
Your data deserves a foundation that’s as resilient as the care you provide to your patients.
Frequently Asked Questions
Is a data center automatically HIPAA compliant if they have a SOC 2 report?
No, a SOC 2 report isn’t a substitute for HIPAA compliance. While SOC 2 Type II audits cover five trust principles, they don’t address all 54 specific safeguards required by the HIPAA Security Rule. You’ll find that SOC 2 provides roughly 90% of the necessary documentation, but you’ve still got to verify the remaining healthcare-specific controls yourself to avoid gaps in your security posture.
Do I need a Business Associate Agreement if the data center staff never touches my servers?
Yes, you’re legally required to have a BAA even if the staff never touches your hardware. The HIPAA Omnibus Rule of 2013 mandates these agreements for any entity with persistent access to the facility. Since they control physical access to your servers, they’re considered a Business Associate. Failing to have one can trigger OCR fines starting at $137 per day for non-compliance.
What are the physical security requirements for a HIPAA-compliant data center?
HIPAA requires strict facility access controls under 45 CFR § 164.310(a)(1). This means your provider must use 24/7 onsite security personnel and multi-factor biometric authentication for every entry point. They’ve also got to keep CCTV recordings for at least 90 days to maintain a clear audit trail of who approached your hardware. These layers ensure that physical PHI access remains strictly regulated.
Can I use public cloud and colocation together for a hybrid HIPAA environment?
You can definitely use a hybrid model as long as both environments meet healthcare data center compliance standards. 82% of healthcare IT leaders now use this approach to keep sensitive PHI on private hardware while using the public cloud for less sensitive workloads. Just make sure your encrypted VPN or direct connect link is also covered in your annual risk assessment.
What happens if my data center provider has a security breach?
Your provider’s required to notify you within 60 days under the HIPAA Breach Notification Rule, though 48 hours is the industry standard for enterprise contracts. If the breach affects more than 500 individuals, you’ve got to notify the Department of Health and Human Services and local media. It’s vital to have a clear incident response plan that’s been tested within the last 12 months.
How often should I audit my colocation provider for healthcare compliance?
You should audit your provider at least once every 12 months to stay compliant with the HIPAA Security Rule’s evaluation standard. Most organizations review the provider’s annual SOC 2 Type II or HITRUST reports instead of doing a manual walkthrough. 74% of compliance managers also perform quarterly reviews of access logs to ensure no unauthorized personnel entered the server cage during that period.
Are remote hands services covered under a standard BAA?
Remote hands services are covered under a standard BAA, but you’ve got to ensure the agreement includes specific language for technicians. Since these workers might physically handle drives or cables, they’re within the scope of PHI protection. Verify that 100% of the data center’s on-site staff has completed HIPAA training within the last year to minimize your organization’s risk profile.
Does HIPAA require data to be encrypted at rest in a data center?
HIPAA technically lists encryption as addressable, but it’s a core requirement for modern healthcare data center compliance in practice. Following NIST Special Publication 800-111 standards for AES-256 encryption protects you from the Breach Notification Rule. If an encrypted drive is lost, it’s generally not considered a reportable breach, which saves your organization from massive legal and PR costs during an audit.
 SUPPORT
SUPPORT


 3EX United States
3EX United States